Denis Doulgeropoulos
Your Financial Professional & Insurance Agent
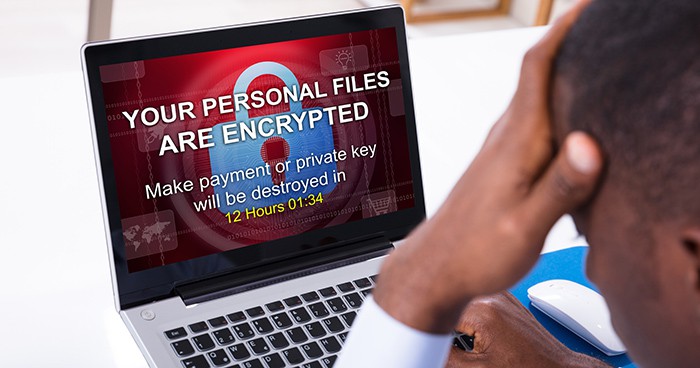
Hostage Data: Ransomware and Protecting Your Digital Information
On May 7, 2021, the Colonial Pipeline, which carries almost half of the East Coast’s fuel supply from Texas to New Jersey, shut down operations in response to a ransomware attack. Colonial paid a $4.4 million ransom not long after discovering the attack, and the pipeline was reopened within a week. While there was enough stored fuel to weather the outage, panic buying caused gasoline shortages on the East Coast and pushed the national average price of gasoline over $3.00 per gallon for the first time since 2014.1
Ransomware Threats to Critical Infrastructure
Ransomware is not a new threat. However, the Colonial Pipeline incident highlighted the serious risks ransomware poses to critical infrastructure and prompted a strong federal response. Notably, the Department of Justice recovered most of the ransom, and the cybercriminal group behind the attack, known as DarkSide, announced it would shut down operations.
Furthermore, the Department of Homeland Security introduced new regulations requiring owners and operators of critical pipelines to report cybersecurity threats within 12 hours of discovery. They must also review their cybersecurity practices and report findings within 30 days. On a broader scale, this incident intensified government efforts to strengthen national cybersecurity and form international coalitions to hold countries that harbor cybercriminals accountable.
Understanding Malicious Code
Ransomware is a form of malicious code, or malware, that infects computer systems and allows attackers to lock files while demanding payment in exchange for a digital key. In some cases, attackers also threaten to release sensitive data. In 2020, an estimated 305 million ransomware attacks occurred worldwide, representing a 62% increase from the previous year. More than 200 million of those attacks targeted systems in the United States.
Recently, high-profile ransomware attacks have revealed a strategic shift. Cybercriminal syndicates now increasingly target organizations essential to public welfare instead of focusing solely on data-rich businesses such as retailers, insurers, and financial firms. For example, shortly after the Colonial Pipeline incident, JBS USA Holdings paid an $11 million ransom following an attack that disrupted one-fifth of the U.S. meat supply.
Additionally, health-care systems have become prime targets due to comparatively low cybersecurity spending, placing patient care at risk. Other frequent targets include state and local governments, school systems, and private companies of all sizes.
Most ransomware groups operate from Russia and other Eastern European countries. They typically set ransom demands based on a victim’s perceived ability to pay. Although the FBI discourages ransom payments, essential organizations may lack the time or resources to rebuild compromised systems. Consequently, paying the ransom may sometimes cost less than system reconstruction.
Protecting Your Data from Ransomware
While major ransomware syndicates pursue high-value targets, many cybercriminals focus on individual consumers. These attackers may lock data, access financial accounts, or steal and sell personal information. Therefore, taking proactive steps to secure your data is essential.
Use Strong Passwords
Strong passwords serve as your first line of defense. Use at least 8 to 12 characters that combine upper- and lower-case letters, numbers, and symbols. Avoid personal information and dictionary words. Although it may be tempting to reuse passwords, using unique credentials for each account significantly improves security.
Consider using a memorable passphrase and adapting it into a complex password. Additionally, a reputable password manager can generate and store secure passwords behind a strong master password. Never share or write down your passwords.
Secure Password Recovery Options
Be cautious when selecting security questions for password recovery. In many cases, fictional answers that you can remember provide better protection, as criminals may guess real answers using publicly available information.
Enable Two-Step Authentication
Two-step authentication adds an extra layer of security by requiring a code sent via text or email. Consequently, even if a password is compromised, unauthorized access becomes more difficult.
Think Before You Click
Ransomware often spreads through phishing emails that trick users into clicking malicious links. Therefore, never click links in emails or texts unless you recognize the sender and understand where the link leads.
Install and Update Security Software
Install antivirus software, firewalls, and email filters, and keep them updated regularly. Outdated software cannot protect against newly developed threats.
Back Up Your Data
Regularly back up your data to an external hard drive. For added protection, disconnect the drive between backups so ransomware cannot access it.
Keep Systems Updated
Use the latest operating system your device supports and install security updates promptly. Many ransomware attacks exploit vulnerabilities in outdated software.
If you encounter a notice claiming your computer is infected or your data is being held for ransom, it is often a fake pop-up. These messages usually include a phone number for “technical support” or payment instructions. Do not click the message or call the number. Instead, close your browser and restart your computer. If problems persist or files are genuinely locked, contact a legitimate technical support provider.
For additional guidance and cybersecurity tips, visit the Cybersecurity & Infrastructure Security Agency website.
This information is not intended as tax, legal, investment, or retirement advice. You are encouraged to consult independent professionals for guidance. The content is based on sources believed to be accurate and does not constitute a solicitation for the purchase or sale of any security. This material was prepared by Broadridge Advisor Solutions. © 2021 Broadridge Financial Solutions, Inc.
